Security Beyond the Network Perimeter
Specialty Services
Hardware, firmware, industrial systems, and physical security, assessed by specialists who understand where digital and physical threats converge.
The Challenge
When Standard Assessments Aren't Enough
Some of your most critical assets don't sit on a traditional network. Hardware devices, IoT systems, industrial controllers, and physical access points require specialized expertise to assess.
Expanding attack surfaces
Connected devices, embedded systems, and operational technology create attack paths that traditional security testing doesn't cover. Adversaries increasingly target these vectors.
Specialized skills required
Hardware reverse engineering, firmware analysis, and physical security assessment demand tooling and expertise that most security consultancies don't possess.
Our Services
Specialty Security Services
Deep technical assessments where digital meets physical.
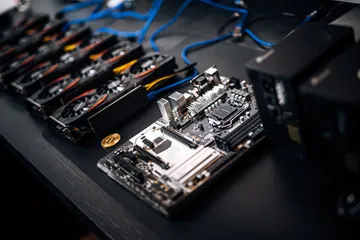
Hardware Security Assessment
Evaluate the security posture of hardware devices: debug interfaces, bus sniffing, chip-level analysis, side-channel assessment, and hardware implant detection.
Firmware & IoT Security
Firmware extraction and analysis, protocol reverse engineering, and vulnerability research for IoT devices, embedded systems, and connected platforms.
Industrial Control Systems (ICS/OT)
Security assessment of SCADA, PLCs, HMIs, and industrial protocols. We understand operational technology environments and test without disrupting production.
Physical Security & Covert Entry
Physical penetration testing, access control assessment, social engineering, and covert entry exercises. Test the security measures that protect your facilities.
Our Difference
What Makes Our Specialty Practice Different
Your Outcomes
What You'll Gain
Complete Threat Picture
Understand your exposure across digital, embedded, and physical attack surfaces, not just the ones covered by standard vulnerability scans.
Actionable Remediation
Detailed findings with practical remediation guidance tailored to your specific hardware, firmware, and physical security infrastructure.
Integrated Defense Strategy
Specialty findings feed into your broader security program, informing detection rules, red team scenarios, and security architecture decisions.
Take the Next Step
Need Specialized Security Assessment?
Tell us about your hardware, embedded systems, or physical security challenges. We'll discuss how our specialty practice can help.
Request a Discovery Call